Hello,
I’m facing an error with the dante-server package on a privileged container and I don’t have this error on an unprivileged container.
Jan 26 18:15:55 test-kali (sh)[510]: danted.service: Failed to set up mount namespacing: Permission denied
Jan 26 18:15:55 test-kali (sh)[510]: danted.service: Failed at step NAMESPACE spawning /bin/sh: Permission denied
Here is how to reproduce it:
incus launch images:debian/14 debforky --ephemeral --config security.privileged=true
incus exec test-kali – apt install dante-server -y
incus exec test-kali – systemctl start danted
Job for danted.service failed because the control process exited with error code.
See "systemctl status danted.service" and "journalctl -xeu danted.service" for details.
About the error:
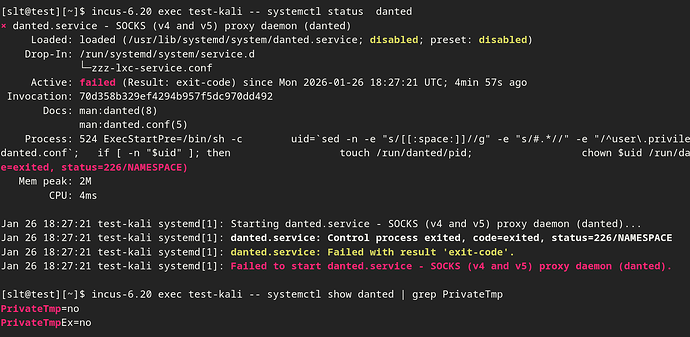
[slt@test][~]$ incus-6.20 exec test-kali -- journalctl -u danted
Jan 26 18:15:55 test-kali systemd[1]: Starting danted.service - SOCKS (v4 and v5) proxy daemon (danted)...
Jan 26 18:15:55 test-kali (sh)[510]: danted.service: Failed to set up mount namespacing: Permission denied
Jan 26 18:15:55 test-kali (sh)[510]: danted.service: Failed at step NAMESPACE spawning /bin/sh: Permission denied
Jan 26 18:15:55 test-kali systemd[1]: danted.service: Control process exited, code=exited, status=226/NAMESPACE
Jan 26 18:15:55 test-kali systemd[1]: danted.service: Failed with result 'exit-code'.
Jan 26 18:15:55 test-kali systemd[1]: Failed to start danted.service - SOCKS (v4 and v5) proxy daemon (danted).
Jan 26 18:27:21 test-kali systemd[1]: Starting danted.service - SOCKS (v4 and v5) proxy daemon (danted)...
Jan 26 18:27:21 test-kali systemd[1]: danted.service: Control process exited, code=exited, status=226/NAMESPACE
Jan 26 18:27:21 test-kali systemd[1]: danted.service: Failed with result 'exit-code'.
Jan 26 18:27:21 test-kali systemd[1]: Failed to start danted.service - SOCKS (v4 and v5) proxy daemon (danted).
I search the internet and found about setting PrivateTmp=false in the systemd override, but from what I can see, this is already set by /run/systemd/system/service.d/zzz-lxc-service.conf:
Any idea on how to debug this?