Ah…that worked! But I am still getting my original problem. I can connect to the webpage at lpc1.streamingworld.us but the iFrame is still not working.
https is not able to connect at all.
http does connect but the iFrame is still not working.
Ray
You got the Let’s Encrypt certificates, what you need now is to copy them to HAProxy and configure HAProxy as a TLS Termination Proxy. That is, your individual websites will not know about TLS and https. All that will be handled by HAProxy.
Your goal is to get your websites fully https, add rules in HAProxy to upgrade to permanent https, and verify that it works.
I did have to re-run a few things. Verifying the haproxy cfg now passes. Here is what I did:
root@HAPROXY:/etc/ssl/lpc1.streamingworld.us# certbot renew --force-renewal --tls-sni-01-port=8888
Saving debug log to /var/log/letsencrypt/letsencrypt.log
Processing /etc/letsencrypt/renewal/lpc1.streamingworld.us.conf
Plugins selected: Authenticator standalone, Installer None
Starting new HTTPS connection (1): acme-v02.api.letsencrypt.org
Renewing an existing certificate
Performing the following challenges:
http-01 challenge for lpc1.streamingworld.us
Waiting for verification…
Cleaning up challenges
new certificate deployed without reload, fullchain is
/etc/letsencrypt/live/lpc1.streamingworld.us/fullchain.pem
Congratulations, all renewals succeeded. The following certs have been renewed:
/etc/letsencrypt/live/lpc1.streamingworld.us/fullchain.pem (success)
and…
haproxy -c -V -f /etc/haproxy/haproxy.cfg
[WARNING] 057/140235 (22886) : Setting tune.ssl.default-dh-param to 1024 by default, if your workload permits it you should set it to at least 2048. Please set a value >= 1024 to make this warning disappear.
Configuration file is valid
So I can access the lpc1 website using https. But again, I am getting blocked at the iFrame I have in the index.html file.
Please visit this site. Maybe it can provide a clue: https://check-your-website.server-daten.de/?q=lpc1.streamingworld.us
There is a difference between https://lpc1.streamingworld.us/ and https://lpc1.streamingworld.us:3000.
Your tests are for the former (port 443) but you need to check for the latter as well.
Currently, https://lpc1.streamingworld.us:3000/ is not responding (Connection refused).
You would need to add some port forwarding to port 3000, etc.
Ok time out. I have a more pressing problem now. I was able to stream rtmp into the host VPS and use haproxy to forward the rtmp to a specific LXD container. But now I can’t do that anymore. I use OBS and it fails to connect to the media server. This has worked for months with no problems but now I am pulling my hair out! I have haproxy running on the host VPS. So haproxy is listening on port 1935, which it is. I can see it trigger when I tail -f haproxy.log and start OBS. But that’s as far as the rtmp is going.
Here is the haproxy.cfg:
global
log /dev/log local0
log /dev/log local1 notice
chroot /var/lib/haproxy
stats socket /run/haproxy/admin.sock mode 660 level admin expose-fd listeners
stats timeout 30s
user haproxy
group haproxy
daemon
maxconn 2048
# Default SSL material locations
ca-base /etc/ssl/certs
crt-base /etc/ssl/private
# Default ciphers to use on SSL-enabled listening sockets.
# For more information, see ciphers(1SSL). This list is from:
# https://hynek.me/articles/hardening-your-web-servers-ssl-ciphers/
# An alternative list with additional directives can be obtained from
# https://mozilla.github.io/server-side-tls/ssl-config-generator/?server=haproxy
ssl-default-bind-ciphers ECDH+AESGCM:DH+AESGCM:ECDH+AES256:DH+AES256:ECDH+AES128:DH+AES:RSA+AESGCM:RSA+AES:!aNULL:!MD5:!DSS
ssl-default-bind-options no-sslv3
defaults
log global
mode tcp
#mode tcp
#option httplog
option dontlognull
#option forwardfor
option http-server-close
timeout connect 5000
timeout client 50000
timeout server 50000
errorfile 400 /etc/haproxy/errors/400.http
errorfile 403 /etc/haproxy/errors/403.http
errorfile 408 /etc/haproxy/errors/408.http
errorfile 500 /etc/haproxy/errors/500.http
errorfile 502 /etc/haproxy/errors/502.http
errorfile 503 /etc/haproxy/errors/503.http
errorfile 504 /etc/haproxy/errors/504.http
# The rtmp is sent from OBS with this url: rtmp://"host IP":1935/LPC1
# So port 1935 equates to container LPC1, 1936 equates to LPC2, etc.
# Currently a proof of concept for 1 container only.
# The container is running a copy of the media server software.
# There is a video player that is a REACT app, runnng on port 3000 of the LPC1 container
# (must be started manually at this time.
frontend LPC1
mode tcp
bind 23.239.31.177:1935
default_backend LPC1-backend
backend LPC1-backend
mode tcp
server LPC1 10.106.37.94:1935
This worked…I swear it did! I could send rtmp from my PC using OBS. When it reached the host VPS, haproxy would forward the rtmp to the media server container and the media server would store the .ts segments as well as create the .m3u8 file, for later viewing
Now when it reaches the haproxy, it does not pass the rtmp to the media server container. Tailing the haproxy.log file, I see the frontend trigger but not the backend.
I am going from good to bad here on this project.
Any ideas how to troubleshoot this issue?
Ray
If haproxy is running in a container, then it cannot bind to IP 23.239.31.177.
That configuration makes sense is haproxy is running on the host.
Yes, this is running on the host. And when I run OBS while tailing the haproxy.log I see this:
Feb 28 08:33:51 localhost haproxy[7862]: Connect from 72.185.92.87:53744 to 23.239.31.177:1935 (LPC1/TCP)
Fixed. Now back to previous issue…playing the video out of the container…
Ray
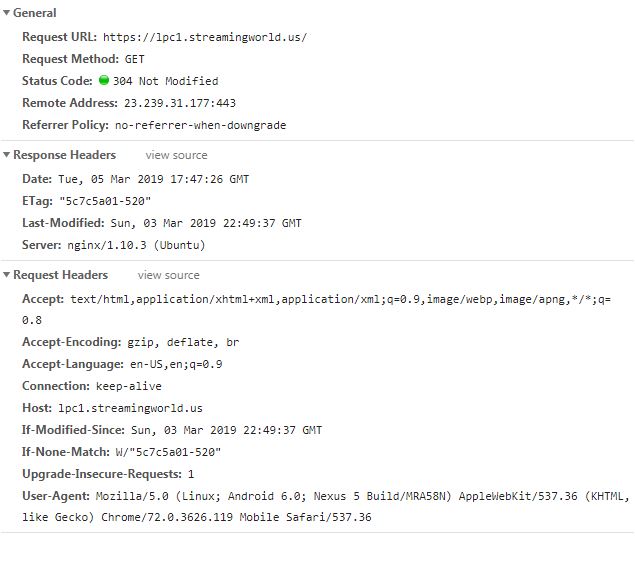
Ok, here are the headers when I try to connect to port 3000 of my container. Do you see anything wrong?
This screen grab is when I browse to the container at https://lpc1.streamingworld…us
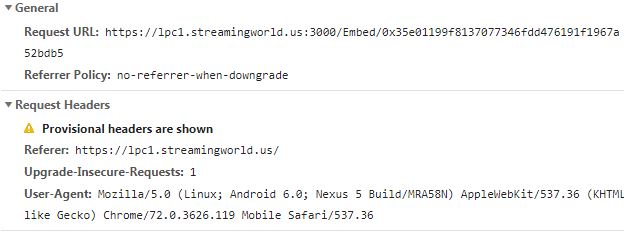
And this one is the iFrame inside the index.html file.:
Appreciate your comments.
Ray
When I try to connect to port 3000, I get Connection refused.
The website (port 443) is good, the problem is with the service at port 3000 which is not accessible from the Internet.
$ telnet lpc1.streamingworld.us 3000
Trying 23.239.31.177...
telnet: Unable to connect to remote host: Connection refused
So, as I have all of the SSL stuff configured for the HAPROXY container, does my nginx container also have to be ssl enabled?
Ray
All websites are served by haproxy as a TLS termination proxy and do not need their own TLS.
However, the port 3000 service probably needs some special care. What software is in there?
It’s a video player.
Does that software support TLS?
Yes it does.
So, in FireFox, I am getting this error:
Secure Connection Failed
An error occurred during a connection to lpc1.streamingworld.us:3000. SSL received a record that exceeded the maximum permissible length. Error code: SSL_ERROR_RX_RECORD_TOO_LONG
Your current implementation does not support properly TLS (i.e. https).
$ openssl s_client -connect lpc1.streamingworld.us:3000
CONNECTED(00000003)
140093691687360:error:1408F10B:SSL routines:ssl3_get_record:wrong version number:../ssl/record/ssl3_record.c:252:
---
no peer certificate available
---
No client certificate CA names sent
---
SSL handshake has read 5 bytes and written 176 bytes
Verification: OK
---
New, (NONE), Cipher is (NONE)
Secure Renegotiation IS NOT supported
Compression: NONE
Expansion: NONE
No ALPN negotiated
SSL-Session:
Protocol : TLSv1.2
Cipher : 0000
Session-ID:
Session-ID-ctx:
Master-Key:
PSK identity: None
PSK identity hint: None
SRP username: None
Start Time: 1551988557
Timeout : 7200 (sec)
Verify return code: 0 (ok)
Extended master secret: no
---
What software are you using? The HTTP header says X-Powered-By: Express, therefore it’s likely nodejs and https://expressjs.com/
Here are the security practices for Express.js, though they do not include an actual link on how to enable TLS.
Here is one such guide on how to add TLS to nodejs, https://www.sitepoint.com/how-to-use-ssltls-with-node-js/ Note that you can either add TLS support in HAProxy or in the container (nodejs).
Additionally, you may also find it easier to add a port-forwarding rule on the host to forward connections to port 3000 (tcp) directly to the container, thus bypassing the proxy. That should make it somewhat easier to configure with nodejs.
I am trying to get it to work with haproxy. On another note what do you think about these results:
https://www.sslshopper.com/ssl-checker.html#hostname=lpc1.streamingworld.us
And here is what I have for port forwarding:
root@localhost:~# iptables -t nat -nvL
Chain PREROUTING (policy ACCEPT 2243 packets, 140K bytes)
pkts bytes target prot opt in out source destination
189 9628 DNAT tcp – eth0 * 0.0.0.0/0 23.239.31.177 tcp dpt:3000 to:10.106.37.15:3000
86 3968 DNAT tcp – eth0 * 0.0.0.0/0 23.239.31.177 tcp dpt:8888 to:10.106.37.15:8888
840 43864 DNAT tcp – eth0 * 0.0.0.0/0 23.239.31.177 tcp dpt:443 to:10.106.37.15:443
22450 1145K DNAT tcp – eth0 * 0.0.0.0/0 23.239.31.177 tcp dpt:80 to:10.106.37.15:80
Chain INPUT (policy ACCEPT 1731 packets, 109K bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 59 packets, 3941 bytes)
pkts bytes target prot opt in out source destination
Chain POSTROUTING (policy ACCEPT 10273 packets, 499K bytes)
pkts bytes target prot opt in out source destination
1342 80520 MASQUERADE all – * * 10.106.37.0/24 !10.106.37.0/24 /* generated for LXD network lxdbr0 */
with .15 being the haproxy container.